We often talk about different technologies, but today we decided to talk on the topic of information security, namely SSL. Everyone knows that certificates provide a reliable connection, and we’ll figure out how this happens and look at the protocols used.
SSL (Secure Sockets Layer) is a cryptographic protocol for secure communication. Since version 3.0, SSL has been replaced with TLS (transport layer security), but the name of the previous version has taken root, so today SSL is most often referred to as TLS.
The purpose of the protocol is to provide secure data transmission. At the same time, asymmetric encryption algorithms are used for authentication (open-private key pair), and symmetric (secret key) for confidentiality preservation. The first type of encryption is more resource-intensive, so its combination with a symmetric algorithm helps to maintain high processing speed.
Handshake
When a user visits a website, the browser requests information about the certificate from the server that sends a copy of the SSL certificate with the public key. Next, the browser checks the certificate, the name of which must match the name of the website.
In addition, the validity date of the certificate is checked and the presence of a root certificate issued by a trusted certification authority. If the browser trusts the certificate, it generates the pre-master secret of the session based on the public key, using the highest level of encryption that both sides support.
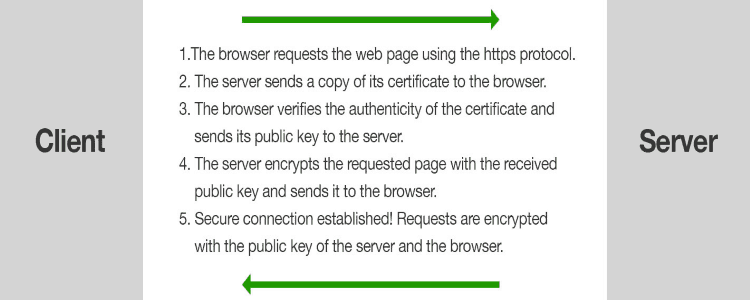
The server decrypts the preliminary secret using its private key, agrees to continue communication and create a shared secret (master secret) using a certain type of encryption. Now both sides use a symmetric key, which is valid only for this session. After it is completed, the key is deleted, and the next time the site is visited, the handshake process is started first.
Encryption Algorithms
For symmetric encryption, different algorithms were used. The first was a block cipher DES, developed by IBM. In the US, it was approved as a standard in the 1970s. The algorithm is based on the Feistel network with 16 cycles. The key length is 56 bits, and the data block is 64 bits.
The development of DES is the 3DES algorithm. It was created to improve the short key in the algorithm of the progenitor. The size of the key and the number of encryption cycles increased three-fold, which reduced the speed of work, but increased reliability.
The most modern is the AES standard, which officially replaced DES in 2002. It is based on the Rijndael block algorithm and its speed is 6 times higher compared to 3DES. The block size here is 128 bits, and the key size is 128/192/256 bits, and the number of rounds of encryption depends on the key size and can be 10/12/14, respectively.
As for asymmetric encryption, it is most often based on algorithms such as RSA, DSA or ECC. RSA (Named in honor of the authors – Rivest, Shamir and Adleman) is used for both encryption and digital signatures. The algorithm is based on the complexity of factoring large numbers and supports all types of SSL certificates.
DSA (Digital Signature Algorithm) is used only to create a digital signature and is based on the computational complexity of taking logarithms in finite fields. For security and performance is completely comparable to RSA.
ECC (Elliptic Curve Cryptography) defines a key pair using points on a curve and is used only for digital signatures. The main advantage of the algorithm is a higher level of reliability with a shorter key length (256-bit ECC-key is comparable in reliability with a 3072-bit RSA-key.
A shorter key also affects the processing time, which is noticeably shortened. This fact and the fact that the algorithm effectively handles a large number of connections made it a convenient tool for working with mobile communications. In SSL certificates, you can use several encryption methods at once for greater protection.
Hash and MAC
The goal of the hash algorithm is to convert the entire content of the SSL certificate into a fixed-length bit string. To encrypt the hash value, the private key of the certification authority is used, which is included in the certificate as a signature.
The hash algorithm also uses the amount needed to verify the integrity of the transmitted data – MAC (message authentication code). The MAC uses the mapping function to represent the message data as a fixed length value, and then hashes the message.
The TLS protocol uses HMAC (hashed message authentication code), which uses a hash algorithm at once with the shared secret key. Here, the key is attached to the data, and to confirm their authenticity, both parties must use the same secret keys, which provides greater security.
All encryption algorithms today support the SHA2 hash algorithm, most often SHA-256. SHA-512 has a similar structure, but the word length is 64 bits (instead of 32), the number of rounds in the cycle is 80 (instead of 64), and the message is divided into blocks of 1024 bits (instead of 512 bits). Previously, the algorithm SHA1 and MD5 was used for the same purposes, but today they are considered vulnerable.
Talks about the refusal of SHA1 were carried out for a long time, but at the end of February the algorithm was officially cracked. Researchers managed to achieve a collision of hashes, that is, the same hash for two different files, which was proved by the insecurity of using the algorithm for digital signatures. The first attempt was made back in 2015, although it was possible to select only those messages, the hash of which coincided. Today we are talking about whole documents.
There Are Various Types of Certificates
Now we have figured out what SSL/TLS is and how its connection occurs, so we can talk about the types of certificates.
Domain Validation, or domain validation certificates, are suitable for non-commercial, small business sites, since they only verifies domain ownership by sending email verification. This type of certificate is the cheapest and most popular.
Organization Validation, or certificates with organization verification, are more reliable, since they confirm the registration data of the company-owner. This information is required to provide the legal entity with the purchase of the certificate, and the certifying center can contact the company directly to confirm this information. The certificate meets RFC standards and contains information about who confirmed it, but the information of the owner is not displayed.
Extended Validation, or a certificate with extended validation, is considered the most reliable SSL certificate. Actually, a green padlock, https before the url, business name displayed in grren text in the browser means exactly that the site has such an EV certificate.
It is necessary for websites that conduct financial transactions and require a high level of confidentiality. However, many sites prefer to redirect users to make payments to external resources, which are confirmed by certificates with extended verification.
In addition, certificates may vary depending on the requirement to secure number of domain names. Single domain certificates (Single Certificate) are tied to secure only one domain. Multi Domain certificates (such as Subject Alternative Name (SAN), Unified Communications Certificate (UCC)) will be effective if has requirment to secure larger number of different domain names and servers.
There are also subdomain certificates known as WildCard SSL certificates that secure all subdomains of the domain name specified during registration. Wildcard SSL certificates are remain cheapest and the best solution, if has requirement to secure only main domain name and its unlimited sub domains.
Sometimes certificates may be required, which will simultaneously include not only several domains, but also subdomains. In such cases, you can purchase certificates such as Positive SSL Multi-Domain, Comodo Multi-Domain Wildcard SSL, where you can also specify the required subdomain names in the list of domains.
Atlast, SSL certificates are one of the most important security solutions to secure data, transffered between web server and the web browser.



