If your business is transitioning to allow more employees to work from home (telecommute), or if you have a sales team that stays connected while on the road, securing information should be a top priority. The British insurance company Lloyd’s estimated in 2015, that cyber attacks would cost businesses up to $400 billion dollars per year. A more recent study conducted by Juniper research, predicts that the acceleration of enterprise records and digitization may bump that loss to over $2.1 trillion dollars by the year 2019.
In this article, we’ll share four important factors that SME to corporate businesses can use, to secure remote device access and protect proprietary information and collateral from hackers. We will also provide some case examples, where normal employee activities may pose a substantial threat to the confidentiality and integrity of the business IT network.
1- Avoid Third-Party Cloud Storage
 Without guidance and regulation from within, employees may feel free to use any kind of third-party digital storage platform to save their work, or resources and information that they need, to conduct daily activities. Because of increased digital fluency, many employees may routinely use cloud services such as Google Drive, or Dropbox.
Without guidance and regulation from within, employees may feel free to use any kind of third-party digital storage platform to save their work, or resources and information that they need, to conduct daily activities. Because of increased digital fluency, many employees may routinely use cloud services such as Google Drive, or Dropbox.
In 2016, The Washington Post reported that the login information (username and passwords) for 68 million Dropbox users, were available for sale on ‘the dark web’. Since people are creatures of habit, the usernames and passwords could be used to attempt access to other networks, including employer data, and banking information. If data belongs to the business, and is confidential or sensitive in nature, a policy prohibiting remote access and uploading to third-party servers should be in place.
2- Reduce or Eliminate BYOD Events
When you want people to work together and collaborate, nothing creates ideas faster than allowing individuals to participate, using their own technology. If your business must provide WiFi access for guests and visitors, it should not be on the same network as internal processes, financial or proprietary information, essential to the operation of the business.
 The ’bring your own device’ events do not have to stop entirely; businesses may set up a guest network to provide internet access, while preserving the integrity of the intranet and private network. The only Wi-Fi password that should be provided is to a secure, non-business guest network to avoid hacking, or the possibility of injected malicious code into the business’ IT ecosystem and environment. Employees should also avoid accessing information through personal devices, such as a smartphone or tablet.
The ’bring your own device’ events do not have to stop entirely; businesses may set up a guest network to provide internet access, while preserving the integrity of the intranet and private network. The only Wi-Fi password that should be provided is to a secure, non-business guest network to avoid hacking, or the possibility of injected malicious code into the business’ IT ecosystem and environment. Employees should also avoid accessing information through personal devices, such as a smartphone or tablet.
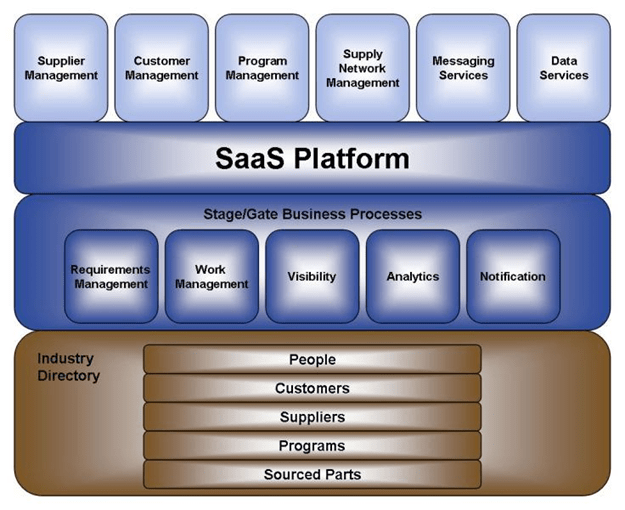
3- Monitor SaaS Platforms for Malicious Content
Did you know that SaaS platforms and B2B applications and ‘free’ software, are 15 times more likely than adult content, to successfully deliver malicious content, from one machine to another? In a security article by Cisco, unmonitored use of unapproved productivity applications (for business or personal use) within corporate environments, represents a substantial risk. The apps can be present on both company issued hardware (such as desktop, tablet or laptop computers), or when an employee utilizes a high-risk app, to access files, emails and other confidential information through their smartphone. A common behavior, particularly for individuals who work outside of normal business hours.
 4- Restrict Wi-Fi Enabled Smartphones
4- Restrict Wi-Fi Enabled Smartphones
Employees with smartphones, who are using the LAN during (or after) business hours, can inadvertently allow their smartphone to become the conduit for a corporate hack. But employees do not have to be onsite, to be exploited for data or communication transmissions, by MITM (man in the middle) attacks. They only need to use their business phone, on public Wi-Fi, while they are on lunch.
A mobile device can be infected with malicious code on a public network, and transfer that code by uploading data from the smartphone, to the business network. It’s that fast, and easy for cyber criminals to be able to not only access your network, but surveil and remove financial, confidential customer contact information, and other valuable data that can be sold on the Dark Web. It can also be used to gain access remotely, to security systems and other onsite opportunities for physical theft on the premises.
 Less than a twenty years ago, the idea of ‘working from home’ was obscure, or something that only CEO’s or business owners had the need and flexibility to do. Today, businesses hire remote workers both for salaried and contract positions, and allow them to work seamlessly by accessing business information and often confidential resources, via VPN or a corporate intranet.
Less than a twenty years ago, the idea of ‘working from home’ was obscure, or something that only CEO’s or business owners had the need and flexibility to do. Today, businesses hire remote workers both for salaried and contract positions, and allow them to work seamlessly by accessing business information and often confidential resources, via VPN or a corporate intranet.
Create an IT security bylaw for employees and management team members, that helps preserve the integrity of the business network, while reducing the risk and loss of confidential information.

 4- Restrict Wi-Fi Enabled Smartphones
4- Restrict Wi-Fi Enabled Smartphones