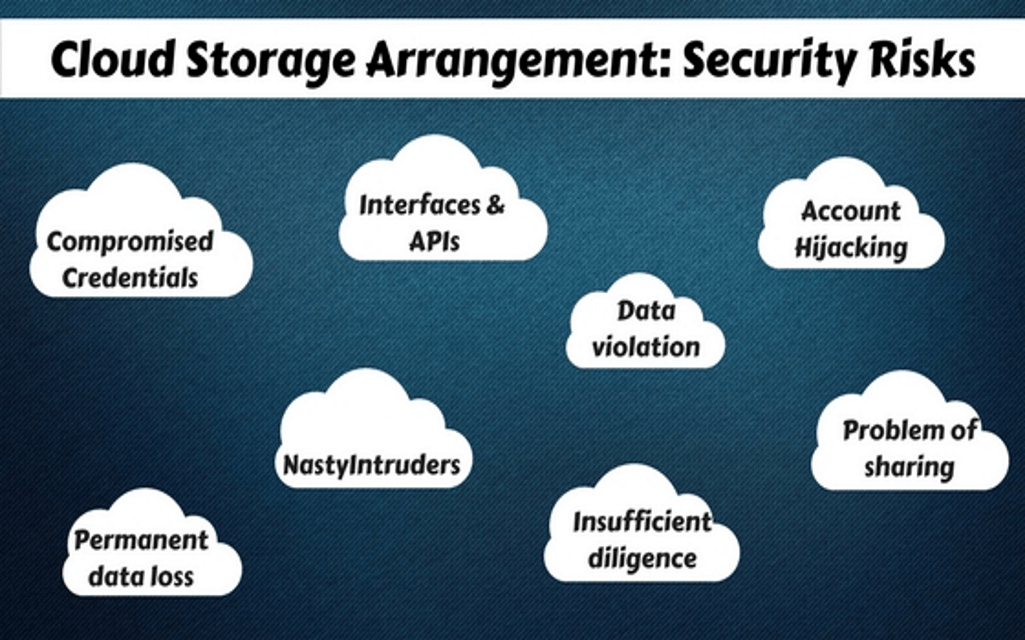
Cloud technology has earned huge popularity worldwide, India is no exception. As per the latest statistics of CSA (Cloud Security Alliance) above 70% of the businesses including Software Company India niche, operate and use cloud services.
According to “Cloud Security Spotlight Report”, advantages like lower static costs, superior flexibility, auto software updates, improved facility of collaboration, and the flexibility to work anytime, anywhere are the fundament reasons business units prefer the use of the cloud. But there is a big BUT. Besides multiple benefits, Cloud has its share of some threats and it is mostly related to security. According to CSA spokesman, cloud security threats are one of the nasty issues detected during 2016 and most of them are still looming large on the digital horizon of the planet, including India. Let’s explore these security risk issues.
Data violation
Could server is used for huge data storage? Therefore hackers are found after these data which may include important client base, financial details, product details, personal details of cloud users, etc. Cloud service providers claim that their security arrangement is of best standard but the rate of data leakage raises a grievance against their bold assurance.
Broken validation challenged and compromised credentials
Clouds server is used for important data storage that often includes authentication key, a weak category of the password, expired the key or invalid validation certificate, etc. Proper ways to implement admin password change, cancellation of authentication, etc. are some of the main reasons for remaining huge amount of data as dumped and unprotected and unsupervised. If these data get divulged, it may create great trouble.
Interfaces and APIs that are hacked
Presently, all cloud service providers offer APIs. IT and Software Company India use interfaces and APIs for managing and interacting with cloud services, including those providers that offer cloud provisioning, orchestration, management, and monitoring. As interfaces and APIs are the highest exposed component of a system they can be accessed from openly by using the internet.
Account hijacking
Cybercrime is getting refined and advanced almost a daily basis. New malicious programs are being introduced almost every day and hackers are trying to manipulate cyber activities by performing fraudulent activities like account hijacking, phishing, identity theft, software exploits, etc. As cloud server contains confidential data and important account details, it often becomes the target of cyber crimes. The vulnerability to cybercrime is a security threat if cloud serves unless data uploaded here is kept under strict surveillance.
Nasty Intruders
Intruders are of different types and they can intrude in cloud server with different purposes like taking revenge, stealing data, which can destroy the whole data storage and related infrastructure. Sometimes encryption and keys should be kept under high protection, and effective monitoring, regular admin audit, logging etc, can control this kind of security breach issue.
Permanent data loss
It is a rare problem due to clouds improvised storage feature but technical glitches are always there. However, in this case, the responsibility of proper storage with adequate backup is the responsibility of the user. Data can be encrypted before storage however in that case if the key gets lost, your data will get lost too. However, with protections like everyday data backup and off-site storage arrangement works like the extra layer of security for the cloud environment.
Insufficient diligence
Every technology has its pros and cons. So is about cloud storage. Before a company or an individual keeps confidential data in cloud storage, the users should understand the technology and its loopholes. In fact, in order to keep data in safe and secured storage, lots of recommendations are suggested by cloud authorities. Before storing data, every user should be diligent enough to implement such precautionary protocols.
Problem of sharing
Sharing is the unique feature of cloud storage and this brings the problem too. Cloud service providers offer sharing mode for infrastructure, platforms, and apps, and if certain susceptibility risk intrudes in any of these shared layers, it affects all users.
These are some of the common cloud abuses that can violate security protocol and introduces hazard for any Software Company India despite their regular surveillance. Some other common risks of cloud server are sudden DDoS attacks, the problem due to uploading of malicious content, as well as the suspicious distribution of spam and phishing emails, etc. However, these minor problems can be sorted easily. For major cloud security risks, users need to hire expert cloud data protection service providers, who can take care of data management with the best possible safety on behalf of its clients.